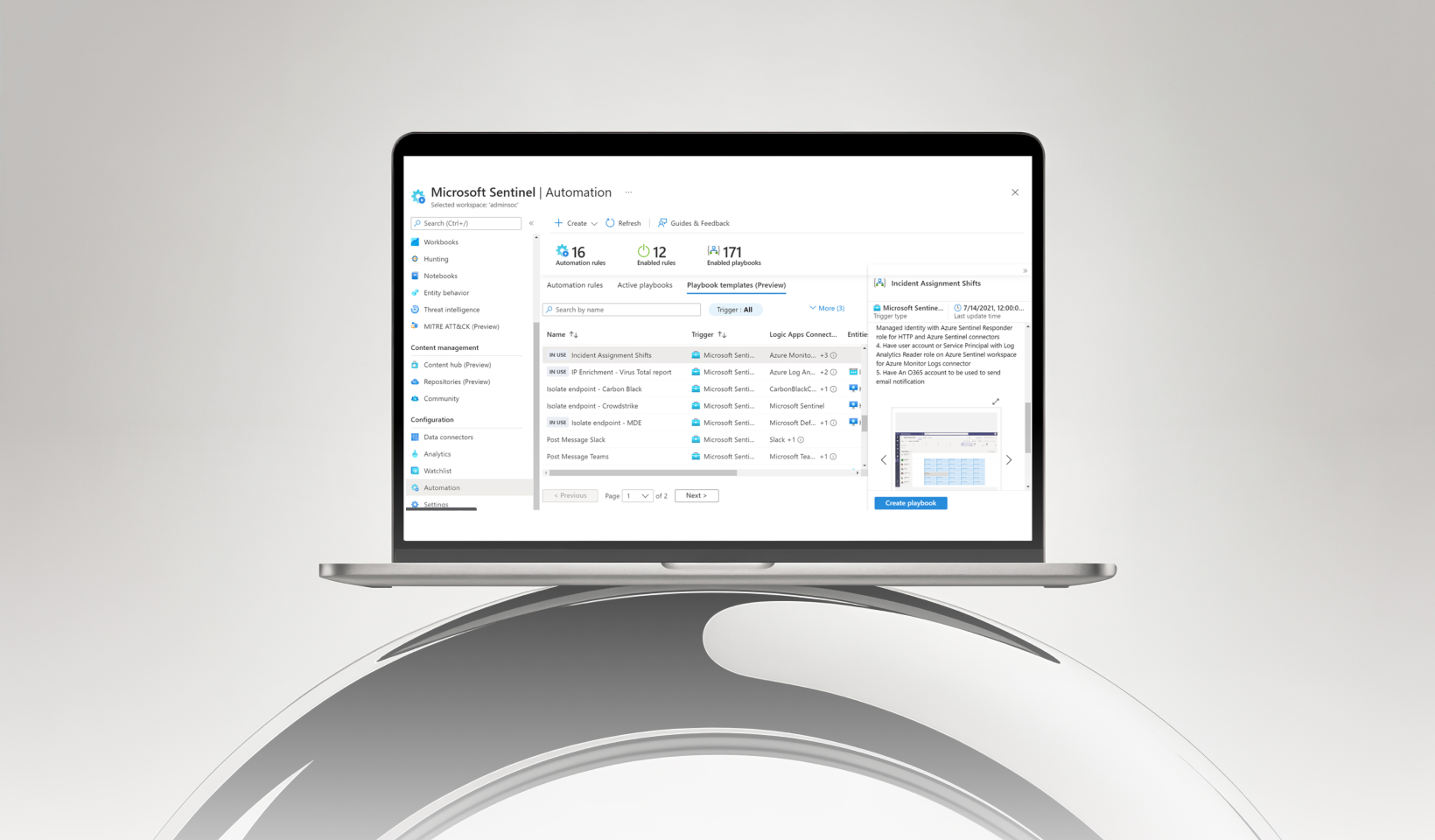
Microsoft has introduced automatic attack disruption capabilities in Microsoft Sentinel
Microsoft has introduced automatic attack disruption capabilities in Microsoft Sentinel that can detect and stop ongoing attacks in AWS environments automatically.
The feature uses AI and rich telemetry from AWS logs ingested into Sentinel to identify attacks like credential compromise and lateral movement faster than traditional manual responses.
When a threat is detected — such as a compromised federated identity or an AWS IAM user, Sentinel (through integration with Microsoft Defender) can automatically revoke sessions, disable accounts, and apply deny policies to contain the attack and prevent further damage. This brings real-time threat response to cloud infrastructure security by turning Sentinel from a passive log analyzer into an active protection tool.
At Chiron IT, we help businesses strengthen their cloud security with Microsoft security solutions that protect across hybrid and multi-cloud environments.
Security should be proactive, not reactive.
www.ChironIT.com
MicrosoftSentinel CloudSecurity AWS CyberSecurity ChironIT